Apple recently introduced Lockdown Mode as a “nuclear option” for digital security. It isn’t meant for everyone, but if you value your privacy above everything else, it is a tool you should know how to use.
🛡️ Quick Security Snapshot
- Main Goal: Stops highly targeted “Zero-Click” digital attacks.
- Key Trade-off: Web browsing will be slower; many attachments will be blocked.
- Verdict: Essential for travel or high-risk privacy needs; overkill for daily casual use.
I’m Swapna Reddy, and I’ve spent the week testing this mode to see what it actually does to the iPhone experience. Here is everything you need to know before you flip the switch.
Causes: Why would you need Lockdown Mode?
Most users don’t need this feature for daily life. However, there are specific situations where enabling it is a smart move:
- Traveling to High-Risk Areas: If you are traveling through international borders or using public WiFi in areas known for digital surveillance.
- Targeted Professions: Journalists, activists, and business executives often use this to prevent “state-sponsored” spyware (like Pegasus) from stealing data.
- Suspicious Activity: If you receive strange, unsolicited FaceTime calls or Message links from unknown international numbers.
- High-Value Data: If your phone contains sensitive legal or financial information that must be protected at all costs.
Precautions: Read this BEFORE turning it on
Because this mode “hardens” your phone, it will feel a bit “broken.” Here are the precautions I recommend:
- Backup Your Data First: Always do a fresh iCloud or computer backup. While the mode is safe, it requires a system reboot.
- Know Your Passcode: You cannot use FaceID/TouchID for the first login after enabling this. Make sure you remember your 6-digit passcode.
- Prepare for Web Glitches: Many websites use custom fonts and complex code to look pretty. Lockdown Mode blocks these, so some sites might look like they are from 1995.
- Work Email Issues: If your job requires you to receive complex attachments via the Messages app, they will likely be blocked. You may need to use a computer for those tasks.
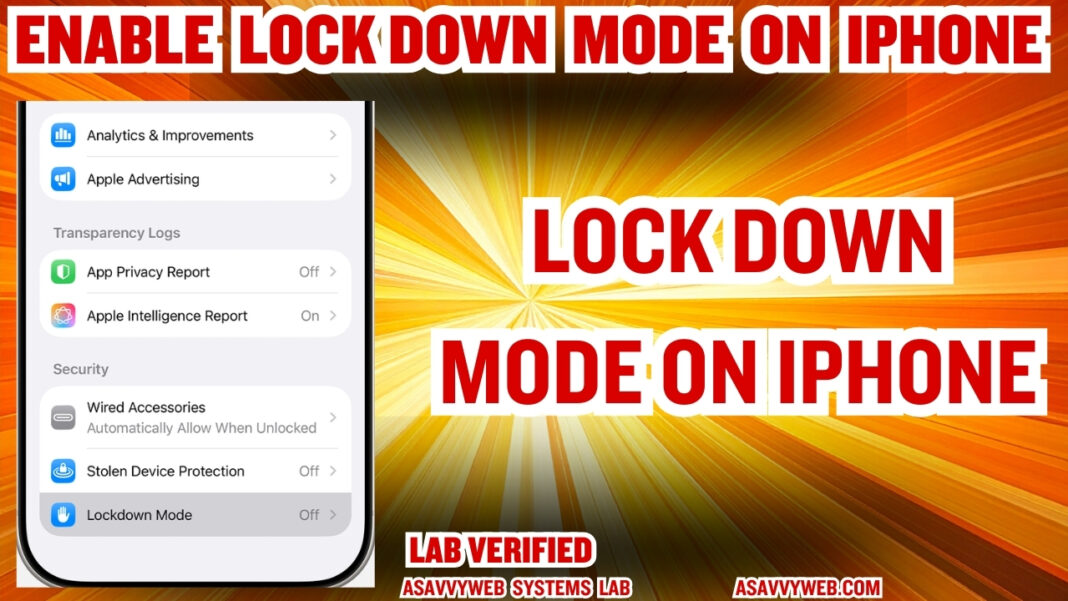
How to Enable Lockdown Mode
- Open Settings on your iPhone.
- Go to Privacy & Security.
- Scroll all the way to the bottom and tap Lockdown Mode.
- Tap Turn On Lockdown Mode.
- Scroll down the explanation page and tap Turn On & Restart.
- Enter your passcode and wait for the phone to reboot.
Expert FAQ (Helpful Tips)
Q: Does it block my normal text messages?
A: No. You can still send and receive text messages and photos. However, links will not show “previews,” and complex file types (like ZIP files) will be blocked.
Q: Will my Apple Watch still work?
A: Yes, but if you enable Lockdown Mode on your iPhone, it will automatically enable it on your paired Apple Watch as well.
Q: Can I turn it off?
A: Yes. You can go back into the same menu at any time and turn it off. The phone will restart again, and everything will go back to the standard, fast experience.